1 What type of connection point is a point of presence (POP)?
between a client and a host
between two local networks
between a computer and a switch
between an ISP and an Enterprise network
2 A network administrator needs to configure Telnet access to a router. Which group of commandsenable Telnet access to the router?
Router(config)# enable password class
Router(config)# line con 0
Router(config-line)# login
Router(config-line)# password cisco
Router(config)# ip host 192.168.1.1 NewYork
Router(config)# enable password cisco
Router(config)# line aux 0
Router(config-line)# login
Router(config-line)# password cisco
Router(config)# enable password class
Router(config)# line vty 0 4
Router(config-line)# login
Router(config-line)# password cisco
3 Which two types of information should be included in a business continuity plan? (Choose two.)
maintenance time periods
intrusion monitoring records
offsite data storage procedures
alternate IT processing locations
problem resolution escalation steps
4 Which two router parameters can be set from interface configuration mode? (Choose two.)
IP address
Telnet password
hostname
console password
subnet mask
enable secret password
5 Which two devices protect a corporate network against malicious attacks at the enterprise edge ?(Choose two.)
demarc
IP security (IPSec)
Data Service Unit (DSU)
intrusion prevention system (IPS)
intrusion detection system (IDS)
6 Which three steps must be performed to remove all VLAN information from a switch but retain therest of the configuration? (Choose three.)
Remove all VLAN associations from the interfaces.
Remove the 802.1q encapsulation from the interface
Issue the command copy start run.
Issue the command delete flash:vlan.dat.
Issue the command erase start.
Reload the switch.
7 What is the demarcation?
physical point where the ISP responsibilty ends and the customer responsibilty begins
physical location where all server farm connections meet before being distributed into the Core
point of entry for outside attacks and is often vulnerable
point of entry for all Access Layer connections from the Distribution Layer devices
8 Which device is responsible for moving packets between multiple network segments?
router
switch
CSU/DSU
IDS device
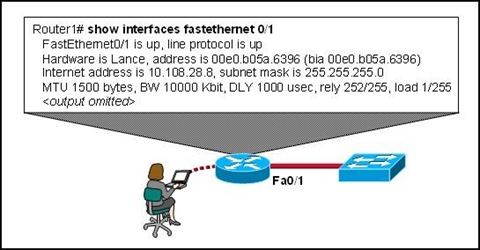
10 What information can an administrator learn using the show version command?
Cisco IOS filename
configured routing protocol
status of each interface
IP addresses of all interfaces
11 Which two situations require a network administrator to use out-of-band management to change arouter configuration? (Choose two.)
Network links to the router are down.
No Telnet password has been configured on the router.
The administrator can only connect to the router using SSH.
The network interfaces of the router are not configured with IP addresses.
Company security policy requires that only HTTPS be used to connect to routers.
12 It is crucial that network administrators be able to examine and configure network devices fromtheir homes. Which two approaches allow this connectivity without increasing vulnerability to externalattacks? (Choose two.)
Configure a special link at the POP to allow external entry from the home computer.
Set up VPN access between the home computer and the network.
Install a cable modem in the home to link to the network.
Configure ACLs on the edge routers that allow only authorized users to access management portson network devices.
Configure a server in the DMZ with a special username and password to allow external access.
13 A network administrator must define specific business processes to implement if a catastrophicdisaster prevents a company from performing daily business routines. Which portion of the networkdocumentation is the administrator defining?
business security plan
business continuity plan
network solvency plan
service level agreement
network maintenance plan
14 A DoS attack crippled the daily operations of a large company for 8 hours. Which two optionscould be implemented by the network administrator to possibly prevent such an attack in the future?(Choose two.)
install security devices with IDS and IPS at the enterprise edge
reset all user passwords every 30 days
filter packets based on IP address, traffic pattern, and protocol
deny external workers VPN access to internal resources
ensure critical devices are physically secure and placed behind the demarc
15 A network manager wants to have processes in place to ensure that network upgrades do not affectbusiness operations. What will the network manager create for this purpose?
business security plan
business continuity plan
service level agreement
network maintenance plan
16 An investment company has multiple servers that hold mission critical datThey are worried that ifsomething happens to these servers, they will lose this valuable information. Which type of plan isneeded for this company to help minimize loss in the event of a server crash?
business security
business continuity
network maintenance
service level agreement
17 When searching for information about authentication methods and usernames of companypersonnel, where can a network administrator look?
Business Continuity Plan
Business Security Plan
Network Maintenance Plan
Service Level Agreement
18 Refer to the exhibit. Which statement is true about port Fa5/1?
When a violation is detected, the port will log the information to a syslog server.
When a violation is detected, the port will go into err-disable mod
There have been 11 security violations since the last reload
The port is currently in the shutdown state.
• Internet, VPN, and WAN modules
• Internet, PSTN, and WAN services
• server farms and network management
• campus infrastructure, including access layer devices
2. In which functional area of the Cisco Enterprise Architecture should IDS and IPS be located to detect
• and prevent services from accessing hosts?
• Enterprise Campus
• Edge Distribution
• Enterprise Edge
• Service Provider Edge
3. A business consultant must use Internet websites to research a report on the e-business strategies of several firms and then electronically deliver the report to a group of clients in cities throughout the world. Which two teleworker tools can the consultant use to accomplish this project? (Choose two.)
• VoIP
• VPN
• HTTP
• Telnet
4. Which two measures help ensure that a hardware problem does not cause an outage in an enterprise LAN that supports mission critical services? (Choose two.)
• providing failover capability
• installing redundant power supplies
• purchasing more bandwidth from the ISP
• implementing broadcast containment with VLANs
• installing routers that can handle a greater amount of throughput
5. Which task would typically only require services located at the access layer of the hierarchical design model?
• connecting to the corporate web server to update sales figures
• using a VPN from home to send data to the main office servers
• printing a meeting agenda on a local departmental network printer
• placing a VoIP call to a business associate in another country
• responding to an e-mail from a co-worker in another department
6. How does a VPN work to support remote user productivity?
• It uses SSL to encrypt remote user logins to the corporate intranet.
• It uses secure Telnet for remote user connections to internal network devices.
• It creates a virtual circuit that allows real-time communications between any two Internet endpoints.
• It uses encapsulation to create a secure tunnel for transmission of data across non-secure networks.****
7. A remote user needs to access a networking device on the internal network of the company. The transactions between the remote user and the device must be secure. Which protocol enables this to happen securely?
• HTTP
• SSH
• Telnet
• FTP
8. What does VoIP provide to telecommuters?
• high-quality, live-video presentations
• real-time voice communications over the Internet
• ability to share desktop applications simultaneously
• secure, encrypted data transmissions through the Internet
9. Which functional component of the Cisco Enterprise Architecture is responsible for hosting internal servers?
• enterprise campus
• enterprise edge
• service provider edge
• building distribution
10. What is the purpose of the Cisco Enterprise Architecture?
• remove the three-layer hierarchical model and use a flat network approach
• divide the network into functional components while still maintaining the concept of Core, Distribution, and Access Layers
• provide services and functionality to the core layer by grouping various components into a single
• component located in the access layer
• reduce overall network traffic by grouping server farms, the management server, corporate intranet, and e-commerce routers in the same layer
11. Which two solutions would an enterprise IT department use to facilitate secure intranet access for remote workers? (Choose two.)
• VPN
• NAT
• user authentication
• client firewall software
• packet sniffing
12. Which statement describes the difference between an enterprise WAN and an enterprise extranet?
• An enterprise WAN is designed to interconnect local LANs, while an enterprise extranet is designed to interconnect remote branch offices.
• An enterprise WAN is designed to interconnect branch offices, while an enterprise extranet is designed to give access to external business partners.
• An enterprise WAN is designed to provide remote access for its teleworkers, while an enterprise extranet is designed to provide Internet connectivity for the enterprise.
• An enterprise WAN is designed to provide Internet connectivity for the enterprise, while an enterprise extranet is designed to provide remote access to the enterprise network for teleworkers.
13. Why would a network administrator want to limit the size of failure domains when designing a network?
• reduces the effect of Ethernet collisions
• reduces the impact of a key device or service failure
• reduces the impact of Internet congestion on critical traffic
• reduces the impact of blocking broadcast packets at the edge of the local network
14. What is the main purpose of the Access Layer in a hierarchically designed network?
• performs routing and packet manipulation
• supplies redundancy and failover protection
• provides a high-speed, low-latency backbone
• serves as a network connection point for end-user devices
15. Which three functions are performed at the Distribution Layer of the hierarchical network model? (Choose three.)
• forwards traffic that is destined for other networks
• isolates network problems to prevent them from affecting the Core Layer
• allows end users to access the local network
• provides a connection point for separate local networks
• transports large amounts of data between different geographic sites
• forwards traffic to other hosts on the same logical network
16. What is a benefit of having an extranet?
• It provides web-like access to company information for employees only.
• It limits access to corporate information to secure VPN or remote access connections only.
• It allows customers and partners to access company information by connecting to a public web server.
• It allows suppliers and contractors to access confidential internal information using controlled external connections.
17. What are two important characteristics or functions of devices at the Enterprise Edge? (Choose two.)
• providing Internet, telephone, and WAN services to the enterprise network
• providing a connection point for end-user devices to the enterprise network
• providing high-speed backbone connectivity with redundant connections
• providing intrusion detection and intrusion prevention to protect the network against malicious activity
• providing packet inspection to determine if incoming packets should be allowed on the enterprise network
18. Why is TCP the preferred Layer 4 protocol for transmitting data files?
• TCP is more reliable than UDP because it requires lost packets to be retransmitted.
• TCP requires less processing by the source and destination hosts than UDP.
• UDP introduces delays that degrade the quality of the data applications.
• TCP ensures fast delivery because it does not require sequencing or acknowlegements.
19. The ABC Corporation implements the network for its new headquarters using the Cisco Enterprise Architecture. The network administrator wants to filter the traffic from and to the outside world. Where should the administrator deploy a firewall device?
• server farm
• enterprise edge
• enterprise campus
• service provider edge
20. Which two statements are reasons why UDP is used for voice and video traffic instead of TCP?(Choose two.)
• TCP requires all data packets to be delivered for the data to be usable.
• The acknowledgment process of TCP introduces delays that break the streams of data.
• UDP does not have mechanisms for retransmitting lost packets.
• UDP tolerates delays and compensates for them.
• TCP is a connectionless protocol that provides end-to-end reliability.
• UDP is a connection-oriented protocol that provides end-to-end reliability.
• authentication
• accreditation
• accounting
• authorization
2. Which three items are normally included when a log message is generated by a syslog client and forwarded to a syslog server? (Choose three.)
• date and time of message
• ID of sending device
• length of message
• message ID
• checksum field
• community ID
3. What is the advantage of using WPA to secure a wireless network?
• It uses a 128-bit pre-shared hexadecimal key to prevent unauthorized wireless access.
• It uses an advanced encryption key that is never transmitted between host and access point.
• It is supported on older wireless hardware, thus providing maximum compatibility with enterprise equipment.
• It requires the MAC address of a network device that is requesting wireless access to be on a list of approved MAC addresses.
4. A company wants to configure a firewall to monitor all channels of communication and allow only traffic that is part of a known connection. Which firewall configuration should be deployed?
• packet filtering
• proxy
• stateful packet inspection
• stateless packet inspection
5. A server log includes this entry: User student accessed host server ABC using Telnet yesterday for 10 minutes. What type of log entry is this?
• authentication
• authorization
• accounting
• accessing
6. What two measures help to verify that server backups have been reliably completed? (Choose two.)
• reviewing backup logs
• performing trial backups
• performing full backups only
• replacing tape backup with hard disk-based backup
• using an autoloader when backups require more than one tape
7. Which means of communication does an SNMP network agent use to provide a network management station with important but unsolicited information?
• query
• broadcast
• ICMP ping
• trap
• poll
8. Which three protocols are used for in-band management? (Choose three.)
• FTP
• HTTP
• SNMP
• Telnet
• TFTP
• DHCP
9. A hacker has gained access to sensitive network files. In analyzing the attack, it is found that the hacker gained access over a wireless segment of the network. It is further discovered that the only security measure in place on the wireless network is MAC Address Filtering. How is it likely that the hacker gained access to the network?
• The hacker used a software tool to crack the shared hexadecimal wireless key.
• The hacker obtained the MAC address of a permitted host, and cloned it on his wireless laptop NIC.
• The attacker mounted a denial of service attack to overwhelm the firewall before penetrating the wireless LAN.
• The hacker gained wireless access to the MAC address database and added his own MAC address to the list of permitted addresses.
10. A network administrator is assigning network permissions to new groups of users and employing the principle of least privilege. Which two actions should the administrator take? (Choose two.)
• Provide users with only the access to resources required to do their jobs.
• Provide the minimum level of permissions required for users to do their jobs.
• Remove all permissions from the users and grant permissions as they are requested.
• Allow users to decide how much permission they need to accomplish their job tasks.
• Provide full access to the users and gradually remove privileges over time.
11. Which three protocols describe methods that can be used to secure user data for transmission across the internet? (Choose three.)
• SMTP
• IPSEC
• SSL
• HTTPS
• FTP
• TFTP
12. Which benefit does SSH offer over Telnet when remotely managing a router?
• encryption
• TCP usage
• authorization
• connection using six VTY lines
13. Which of the following does SNMP use to hold information collected about the network?
• network management station
• network management database
• management information base
• database information agent
14. What are two potential problems with using tape media to back up server data? (Choose two.)
• Tape is not a cost-effective means of backing up data.
• Data tapes are difficult to store offsite.
• Data tapes are prone to failure and must be replaced often.
• Tape drives require regular cleaning to maintain reliability.
• Backup logs are not available with tape backup solutions.
15. What is the term for the public network between the boundary router and the firewall?
• "clean" LAN
• intranet
• DMZ
• extranet
16. Which two characteristics of network traffic are being monitored if a network technician configures the company firewall to operate as a packet filter? (Choose two.)
• applications
• physical addresses
• packet size
• ports
• protocols
17. When is the use of out-of-band network management necessary?
• when a server needs to be monitored across the network
• when the management interface of a device is not reachable across the network
• when enhanced monitoring features are required to gain an overall view of the entire network
• when it is desirable to use the information that is provided by SNMP
18. What network layer security protocol can secure any application layer protocol used for communication?
• HTTPS
• IMAP
• FTPS
• IPSEC
• TLS
19. Before a technician upgrades a server, it is necessary to back up all data. Which type of backup is necessary to ensure that all data is backed up?
• daily
• differential
• full
• incremental
• partial
20. What AAA component assigns varying levels of rights to users of network resources?
• auditing
• accounting
• authorization
• access control
• authentication
• acknowledgement
• The two bottom layers of the TCP/IP model make up the bottom layer of the OSI model.
• The TCP/IP model is a theoretical model and the OSI model is based on actual protocols.
• The OSI network layer is comparable to the Internet layer of the TCP/IP model.
• The TCP/IP model specifies protocols for the physical network interconnection.
• The TCP/IP model is based on four layers and the OSI model is based on seven layers.
2. To meet customer expectations, an ISP must guarantee a level of service that is based on what two factors? (Choose two.)
• accessibility
• adaptability
• availability
• reliability
• scalability
3. User1 is sending an e-mail to User2@cisco.com. What are two characteristics of the process of sending this data? (Choose two.)
• It utilizes TCP port 110.
• A TCP connection is established directly between the User1 and User2 client computers in order to send the e-mail message.
• It utilizes a store and forward process.
• The same application layer protocol is used to send the e-mail and retrieve it from the destination server.
• SMTP is used to send the e-mail message to the mail servers.
4. Refer to the exhibit. Host1 is in the process of setting up a TCP session with Host2. Host1 has sent a SYN message to begin session establishment. What happens next?
• Host1 sends an ACK message to Host2.
• Host1 sends a SYN message to Host2.
• Host1 sends a SYN-ACK message to Host2.
• Host2 sends an ACK message to Host1.
• Host2 sends a SYN message to Host1.
• Host2 sends a SYN-ACK message to Host1.
5. What are three characteristics of network reliability? (Choose three.)
• Redundant hardware provides enhanced reliability.
• Reliability is measured as a percent.
• Reliability is the responsibility of the ISP customers.
• Fault tolerance is a measure of reliability.
• The longer the MTBF, the greater the reliability.
6. Which two statements describe the FTP protocol? (Choose two.)
• It uses well-known port 23.
• The protocol interpreter is responsible for the data transfer function.
• In passive data connections, the FTP client initiates the transfer of data.
• It requires two connections between client and server.
• FTP servers open a well-known port on the client machine.
7. What is the function of the TCP three-way handshake?
• It enables the synchronization of port numbers between source and destination hosts.
• It immediately triggers the retransmission of lost data.
• It synchronizes both ends of a connection by allowing both sides to agree upon initial sequence numbers.
• It identifies the destination application on the receiving host.
8. What are three characteristics of HTTPS? (Choose three.)
• It uses a different client request-server response process than HTTP uses.
• It specifies additional rules for passing data between the application and data link layers.
• It supports authentication.
• It allows more simultaneous connections than HTTP allows.
• It encrypts packets with SSL.
• It requires additional server processing time.
9. Which DNS zone resolves an IP address to a qualified domain name?
• dynamic lookup
• forward lookup
• resolution lookup
• reverse lookup
10.
What type of update allows client computers to register and update their resource records with a DNS server whenever changes occur?
• dynamic
• zone transfer
• local recursive query
• root domain query
• top-level domain query
11. Refer to the exhibit. Which two statements are true about this file? (Choose two.)
• If the gateway address changes, the file will be updated dynamically.
• The command ping fileserv will use IP address 172.16.5.10.
• If the ping www.cisco.com command is issued, the file will be checked for the Cisco web server IP address before DNS is queried.
• The file must be created by the user if it is to be used by a workstation.
• Name to IP address mappings are added to the file after they are received from DNS.
12. Which two tasks are the responsibility of the local DNS server? (Choose two.)
• maintaining a large number of cached DNS entries
• maintaining the ISP server
• mapping name-to-IP addresses for internal hosts
• forwarding name resolution requests to a caching-only server
• forwarding all name resolution requests to root servers on the Internet
13. What are three unique characteristics of UDP? (Choose three.)
• connection oriented
• full-duplex operation
• low overhead
• no flow control
• no error-recovery function
• reliable transmission
14. A manufacturing company is looking into subscribing to services from a new ISP. The company requires hosted world wide web, file transfer, and e-mail services. Which three protocols represent the key application services that are required by the company? (Choose three.)
• FTP
• HTTP
• ICMP
• PPP
• Telnet
• SMTP
15. Which two options correctly match protocol and well-known port number? (Choose two.)
• DNS - 25
• FTP - 110
• HTTP - 80
• POP3 - 25
• SMTP - 25
16. Within TCP, what combination makes up a socket pair?
• source port with destination port
• source IP address with destination port
• source IP address and destination IP address
• source IP address and port with a destination IP address and port
17. Which protocol is used to send e-mail, either from a client to a server or from a server to another server?
• SNMP
• FTP
• SMTP
• HTTPS
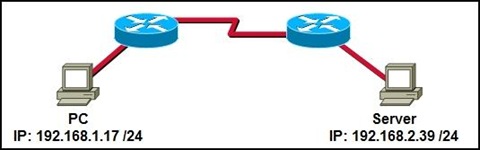
18. Refer to the exhibit. The PC is requesting HTTP data from the server. What is a valid representation of source and destination sockets for this request?
• Source - 192.168.1.17:80 ; Destination - 192.168.2.39:80
• Source - 192.168.1.17:80 ; Destination - 192.168.2.39:1045
• Source - 192.168.1.17:1045 ; Destination - 192.168.2.39:80
• Source - 192.168.1.17:1045 ; Destination - 192.168.2.39:1061
19. What type of DNS server is typically maintained by an ISP?
• caching-only
• root
• second-level
• top-level
20. A client is communicating with a server on a different segment of the network. How does the server determine what service is being requested by the client?
• The server will apply the default service configured in directory services.
• The server will use ARP to discover the appropriate service from the local router.
• The server will send a request to the client asking for the appropriate service.
• The server will determine the appropriate service from the destination port field.
21.
When a host is communicating with multiple applications on the same server at the same time, which of the following will have the same value for each session? (Choose two.)
• IP address
• MAC address
• session number
• sequence number
• show version
• show ip route
• show interface
• show ip protocols
2.

Refer to the exhibit. What is the maximum number of RIP routers that could separate HostA and HostB and still leave the hosts with connectivity to each other?
• 14
• 15
• 16
• 17
3. In which situation would a company register for its own autonomous system number (ASN)?
• when the company's ISP adds connection points to the Internet
• when additional routers are added to the corporate internetwork
• when more than one interior routing protocol is used
• when the company uses two or more ISPs
4. Consider this routing table entry
• R 172.16.1.0/24 [120/1] via 200.1.1.1 00:00:27 Serial0/1
• What type of route is this?
• a static route
• a default route
• a RIP route
• an OSPF route
• an EIGRP route
• a directly-connected route
5. What is the difference between interior and exterior routing protocols?
• Exterior routing protocols are only used by large ISPs. Interior routing protocols are used by small ISPs.
• Interior routing protocols are used to route on the Internet. Exterior routing protocols are used inside organizations.
• Exterior routing protocols are used to administer a single autonomous system. Interior routing protocols are used to administer several domains.
• Interior routing protocols are used to communicate within a single autonomous system. Exterior routing protocols are used to communicate between multiple autonomous systems.
6. What information is included in RIPv2 routing updates that is not included in RIPv1 updates?
• metric
• subnet mask
• area identification
• hop count
• autonomous system number
7. Which routing protocol is used to exchange data between two different ISPs?
• BGP
• EIGRP
• OSPF
• RIP v2
8.
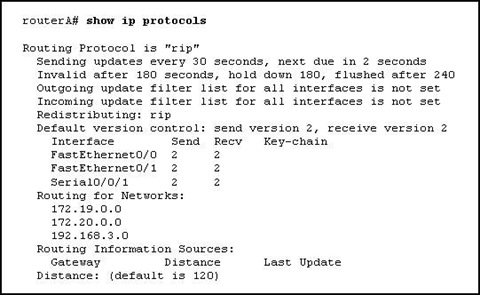
Refer to the exhibit. Which configuration command or commands contributed to the output that is shown?
• routerA(config-router)# no version 2
• routerA(config)# interface fa0/0
• routerA(config-if)# ip address 172.19.0.0 255.255.0.0
• routerA(config-router)# network 192.168.3.0
• routerA(config)# no ip default-gateway
9.

Refer to the exhibit. If all routers are running RIP and network 10.0.0.0 goes down, when will R3 learn that the network is no longer available?
• in 30 seconds
• in 60 seconds
• in 90 seconds
• Immediately
10. What statement is true regarding an AS number?
• AS numbers are controlled and registered for Internet use.
• Interior routing protocols require registered AS numbers.
• ISPs require all customers to have registered AS numbers.
• All routers at an ISP must be assigned the same AS number.
11. What is the purpose of the network command used when configuring RIP?
• to specify whether RIPv1 or RIPv2 will be used as the routing protocol
• to allow the router to monitor RIP updates that occur on other routers
• to identify which networks on the router will send and receive RIP updates
• to configure the IP address on an interface that will use RIP
• to identify all of the remote networks that should be reachable from the router
12. Which command would a network administrator use to determine if the routers in an enterprise have learned about a newly added network?
• router# show ip address
• router# show ip route
• router# show ip networks
• router# show ip interface brief
• router# debug ip protocol
• router# debug rip update
13. What is the purpose of a routing protocol?
• It is used to build and maintain ARP tables.
• It provides a method for segmenting and reassembling data packets.
• It allows an administrator to devise an addressing scheme for the network.
• It allows a router to share information about known networks with other routers.
• It provides a procedure for encoding and decoding data into bits for packet forwarding.
14. What device enables an ISP to connect with other ISPs to transfer data?
• border gateway router
• DSLAM
• web server
• interior router
15. Which command will display RIP routing updates as they are sent and received?
• show ip route
• show ip rip
• debug ip rip
• show ip protocols
• show ip rip database
16. Which part of an IP packet does the router use to make routing decisions?
• source IP address
• source MAC address
• destination IP address
• destination MAC address
17. What two types of businesses would benefit from registering as their own autonomous systems? (Choose two.)
• a home business with one ISP connection
• a global business with connections to multiple local ISPs
• a medium-sized nationwide business with Internet connectivity through different ISPs
• a large enterprise with two connections to the same ISP
• a small ISP with a single Internet connection through a larger ISP
18. Which command will display RIP activity as it occurs on a router?
• debug ip rip
• show ip route
• show ip interface
• show ip protocols
• debug ip rip config
• show ip rip database
19. Why is fast convergence desirable in networks that use dynamic routing protocols?
• Routers will not allow packets to be forwarded until the network has converged.
• Hosts are unable to access their gateway until the network has converged.
• Routers may make incorrect forwarding decisions until the network has converged.
• Routers will not allow configuration changes to be made until the network has converged.
20. Which two statements describe static routes? (Choose two.)
• They are created in interface configuration mode.
• They require manual reconfiguration to accommodate network changes.
• They automatically become the default gateway of the router.
• They are identified in the routing table with the prefix S
• They are automatically updated whenever an interface is reconfigured or shutdown.
21. Which two statements or sets of statements describe differences between link-state and distance vector routing protocols? (Choose two.)
• Link-state routing protocols routinely use more bandwidth for updates than do distance vector routing protocols.
• Distance vector routing protocols update all routers at one time. Link-state routing protocols update one router at a time.
• Link-state routers only know about directly connected routers. Distance vector routers know about every router in the network.
• Link-state routing protocols update when a change is made. A network using distance vector routing protocols only updates at a specific interval.
• Distance vector routing protocols have limited information about the entire network. Link state routing protocols know about all routers in the network.
• In case of similar topologies, networks using link-state routing protocols typically converge more rapidly than do networks using distance vector routing protocols.
22. Which protocol is an exterior routing protocol?
• BGP
• EIGRP
• OSPF
• RIP
23. Hosts on two separate subnets cannot communicate. The network administrator suspects a missing route in one of the routing tables. Which three commands can be used to help troubleshoot Layer 3 connectivity issues? (Choose three.)
• Ping
• show arp
• Traceroute
• show ip route
• show interface
• show cdp neighbor detail
24. What term refers to a group of networks that uses the same internal routing policies and is controlled by a single administrative authority?
• Internet
• intranet
• virtual private network
• autonomous system
1. In an 8 bit binary number, what is the total number of combinations of the eight bits?
• 128
• 254
• 255
• 256
• 512
• 1024
2. Convert the decimal number 231 into its binary equivalent. Select the correct answer from the list below.
• 11110010
• 11011011
• 11110110
• 11100111
• 11100101
• 11101110
3. How many usable hosts are available given a Class C IP address with the default subnet mask?
• 254
• 255
• 256
• 510
• 511
• 512
4. Which statement describes NAT overload or PAT?
• Each internal address is dynamically translated to an individual external IP address.
• A single internal address is always translated to the same unique external IP address.
• Many internal addresses can be translated to a single IP address using different port assignments.
• Many internal addresses are statically assigned a single IP address and port to use for communications.
5. Which IPv4 class of addresses provides the most networks?
• Class A
• Class B
• Class C
• Class D
• Class E
6. Which statement accurately describes public IP addresses?
• Public addresses cannot be used within a private network.
• Public IP addresses must be unique across the entire Internet.
• Public addresses can be duplicated only within a local network.
• Public IP addresses are only required to be unique within the local network.
• Network administrators are free to select any public addresses to use for network devices that access the Internet.
7. Which two statements describe classful IP addresses? (Choose two.)
• It is possible to determine which class an address belongs to by reading the first bit.
• The number of bits used to identify the hosts is fixed by the class of the network.
• Only Class A addresses can be represented by high-order bits 100.
• Up to 24 bits can make up the host portion of a Class C address.
• Up to 24 bits can be used to identify unique networks.
• Three of the five classes of addresses are reserved for multicasts and experimental use.
8. Company XYZ uses a network address of 192.168.4.0. It uses the mask of 255.255.255.224 to create subnets. What is the maximum number of usable hosts in each subnet?
• 6
• 14
• 30
• 62
9. hat is the network broadcast address for a Class C address of 192.168.32.0 with the default subnet mask?
• 192.168.0.0
• 192.168.0.255
• 192.168.32.0
• 192.168.32.254
• 192.168.32.255
10. 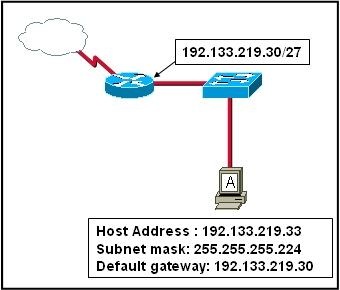
Refer to the exhibit. Host A is connected to the LAN, but it cannot get access to any resources on the Internet. The configuration of the host is shown in the exhibit. What could be the cause of the problem?
• The host subnet mask is incorrect.
• The default gateway is a network address.
• The default gateway is a broadcast address.
• The default gateway is on a different subnet from the host.
11. IPv6 increases the IP address size from 32 bits to how many bits?
• 64
• 96
• 128
• 192
• 256
• 512
12. What is the range of the first octet in a Class B address?
• 127 to 191
• 127 to 192
• 128 to 191
• 128 to 192
13. Which IPv4 class provides the highest number of host addresses per network?
• Class A
• Class B
• Class C
• Class D
• Class E
14. 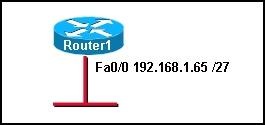
refer to the exhibit. Which range of IP addresses would allow hosts that are connected to the Router1 Fa0/0 interface to access outside networks?
• 192.168.1.0 through 192.168.1.95
• 192.168.1.66 through 192.168.1.94
• 192.168.1.66 through 192.168.1.96
• 192.168.1.0 through 192.168.1.127
• 192.168.1.66 through 192.168.1.128
15. Which option shows the proper notation for an IPv6 address?
• 2001,0db8,3c55,0015,abcd,ff13
• 2001-0db8-3c55-0015-abcd-ff13
• 2001.0db8.3c55.0015.abcd.ff13
• 2001:0db8:3c55:0015::abcd:ff13
16. What are two reasons that NAT was developed? (Choose two.)
• to preserve registered public IP addresses
• to allow users on the public Internet to access local networks
• to provide a method for privately addressed LANs to participate in the Internet
• to make routing protocols operate more efficiently
• to allow private addresses to be routed on the public Internet
• to reduce overhead and CPU usage on gateway routers
17. What must happen for a privately addressed host on an inside local network to be able to communicate with an outside destination host on the Internet?
• The host IP address must be translated to an outside private address.
• The host IP address must be translated to an inside local address.
• The host IP address must be translated to an outside local address.
• The host IP address must be translated to an inside global address.
18. Which port numbers are used by PAT to create unique global addresses?
• 255 and below
• 1024 and below
• 1025 and above
• 64,000 and above
19. Static NAT works by mapping a specific inside local IP address to what other specific address type?
• inside global
• outside local
• outside global
• private IP address
20. What are three advantages of NAT implementations? (Choose three.)
• improved security
• improved router performance
• decreased processor load
• improved scalability
• universal application compatibility
• sharing few public IP addresses with many hosts
• SDM is used for in-band management only. The IOS CLI can be used for in-band and out-of-band management.
• SDM is accessed through a Telnet application. The IOS CLI is accessed through a web browser.
• SDM is available for all router platforms. The IOS CLI is available for a limited number of Cisco devices.
• SDM utilizes GUI buttons and text boxes. The IOS CLI requires the use of text-based commands.
• SDM is used for advanced configuration tasks. The IOS CLI is preferred for initial basic device configuration.
2. Which mode will a configured router display at login?
• global configuration mode
• setup mode
• ROM monitor mode
• user EXEC mode
3.
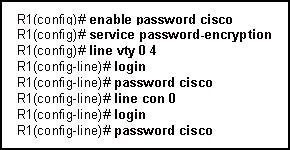
Refer to the exhibit. Which password or passwords will be encrypted as a result of the configuration that is shown?
• virtual terminal only
• enable mode only
• console and virtual terminal only
• enable mode and virtual terminal
• only the service password
• all configured passwords
4.
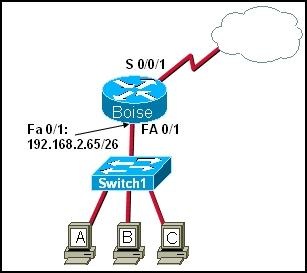
Refer to the exhibit. Which three sets of commands are required to enable administrators to connect to the Switch1 console over Telnet for configuration and management? (Choose three.)
• Switch1(config)# interface fa0/1
Switch1(config-if)# ip address 192.168.2.64 255.255.255.192
• Switch1(config)# interface fa0/1
Switch1(config-if)# ip address 192.168.2.66 255.255.255.192
• Switch1(config)# interface vlan 1
Switch1(config-if)# ip address 192.168.2.126 255.255.255.192
Switch1(config-if)# no shutdown
• Switch1(config)# line vty 0 4
Switch1(config-line)# enable password cisco
Switch1(config-line)# login
• Switch1(config)# line vty 0 15
Switch1(config-line)# password cisco
Switch1(config-line)# login
• Switch1(config)# ip default-gateway 192.168.2.65
5. How does the SYST LED on the catalyst 2960 switch indicate a POST failure?
• blinks rapidly amber
• blinks rapidly green
• steady amber
• steady green
6.

Refer to the exhibit. A company always uses the last valid IP address in a subnetwork as the IP address of the router LAN interface. A network administrator is using a laptop to configure switch X with a default gateway. Assuming that the switch IP address is 192.168.5.147/24, what command will the administrator use to assign a default gateway to the switch?
• X(config)# ip default-gateway 192.168.5.254
• X(config)# ip gateway 192.168.5.1
• X(config)# ip route 0.0.0.0 0.0.0.0 192.168.5.1
• X(config)# ip default-route 192.168.5.1
• X(config)# ip route 192.168.5.254 255.255.255.0 fastethernet 0/0
7. A technician has made changes to the configuration of a router. What command will allow the technician to view the current configuration before he saves the changes?
• router# show running-config
• router# show startup-config
• router# show flash
• router# show version
8. Passwords can be used to restrict access to all or parts of the Cisco IOS. Select the modes and interfaces that can be protected with passwords. (Choose three.)
• VTY interface
• console interface
• Ethernet interface
• secret EXEC mode
• privileged EXEC mode
• router configuration mode
9. To save time, IOS commands may be partially entered and then completed by typing which key or key combination?
• Tab
• Ctrl-P
• Ctrl-N
• Up Arrow
• Right Arrow
• Down Arrow
10. What is the correct command sequence to configure a router host name to 'LAB_A'?
• Router> enable
Router# configure terminal
Router(config)# hostname LAB_A
• Router> enable
Router# hostname LAB_A
• Router> enable
Router# configure router
Router(config)# hostname LAB_A
• Router> enable
Router(config)# host name LAB_A
11.
Refer to the exhibit. From the router console, an administrator is unable to ping a Catalyst switch that is located in another building. What can the administrator do from her location to check the IP configuration of the attached switch?
• Open an SDM session with the switch from her desktop.
• Telnet to the switch from the router console.
• Use the show cdp neighbors detail command from the router console.
• The administrator must go to the switch location and make a console connection to check these settings.
12. Which two options must be selected in SDM Express to enable a router serial interface to obtain an IP address automatically? (Choose two.)
• Easy IP (IP negotiated)
• IP unnumbered
• No IP address
• HDLC encapsulation
• Frame Relay encapsulation
• PPP encapsulation
13. What three settings can be made in the SDM Express basic configuration screen? (Choose three.)
• host name
• DHCP options
• domain name
• interface IP addresses
• enable secret password
• DNS server IP addresses
14. Which tasks can be accomplished by using the command history feature? (Choose two.)
• View a list of commands entered in a previous session.
• Recall up to 15 command lines by default.
• Set the command history buffer size. • Recall previously entered commands.
• Save command lines in a log file for future reference.
15. What option within Cisco SDM Express must be configured to allow hosts that receive IP address settings from the router to resolve names on the network or Internet?
• host name
• domain name
• DHCP address pool
• DNS server IP address
16. Which three encapsulation types can be set on a serial interface by an administrator who is using SDM Express? (Choose three.)
• ATM
• CHAP
• Frame Relay
• HDLC
• PAP
• PPP
17. Which command will display routing table information about all known networks and subnetworks?
• Router# show ip interfaces
• Router# show ip connections
• Router# show ip route
• Router# show ip networks
18. A network administrator needs to configure a router. Which of the following connection methods requires network functionality to be accessible?
• console
• AUX
• Telnet
• modem
19. Which three pieces of information about a neighbor device can be obtained by the show cdp neighbors command? (Choose three.)
• platform
• routing protocol
• connected interface of neighbor device
• device ID
• IP addresses of all interfaces
• enable mode password
20.

Which function is a unique responsibility of the DCE devices shown in the exhibit?
• transmission of data
• reception of data
• clocking for the synchronous link
• noise cancellation in transmitted data
21. Which of the following are functions of NVRAM? (Choose two.)
• stores the routing table
• retains contents when power is removed
• stores the startup configuration file
• contains the running configuration file
• stores the ARP table
22.
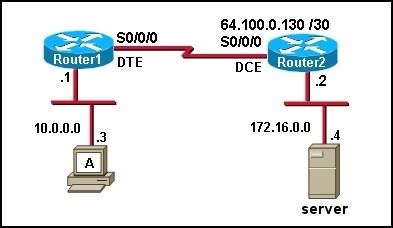
Refer to the exhibit. Which series of commands will enable users who are attached to Router1 to access the remote server?
• Router1(config)# interface S0/0/0
Router1(config-if)# ip address 64.100.0.129 255.255.255.252
Router1(config-if)# clock rate 64000
Router1(config-if)# no shutdown
• Router1(config)# interface S0/0/0
Router1(config-if)# ip address 64.100.0.125 255.255.255.252
Router1(config-if)# no shutdown
• Router1(config)# interface S0/0/0
Router1(config-if)# ip address 64.100.0.125 255.255.255.252
Router1(config-if)# clock rate 64000
Router1(config-if)# no shutdown
• Router1(config)# interface S0/0/0
Router1(config-if)# ip address 64.100.0.129 255.255.255.252
Router1(config-if)# no shutdown
23. A network technician is attempting to add an older workstation to a Cisco switched LAN. The technician has manually configured the workstation to full-duplex mode in order to enhance the network performance of the workstation. However, when the device is attached to the network, performance degrades and excess collision are detected. What is the cause of this problem?
• The host is configured in a different subnet from the subnet of the switch.
• There is a duplex mismatch between the workstation and switch port.
• The switch port is running at a different speed from the speed of the workstation NIC.
• The host has been configured with a default gateway that is different from that of the switch.
24. Which of the following statements are true regarding the user EXEC mode? (Choose two.)
• All router commands are available.
• Global configuration mode can be accessed by entering the enable command.
• A password can be entered to allow access to other modes.
• Interfaces and routing protocols can be configured.
• Only some aspects of the router configuration can be viewed.
25. Which command turns on a router interface?
• Router(config-if)# enable
• Router(config-if)# no down
• Router(config-if)# s0 active
• Router(config-if)# interface up
• Router(config-if)# no shutdown


